Cloud vs. On-Premise Security: Why Cloud Surveillance Is More Secure

Most IT managers who run on-premise NVR or DVR systems can name the last time they patched their email server. Few can say the same about their camera firmware. That gap, between the security attention given to IT systems and the maintenance actually applied to physical security hardware, is where real-world exploits land. Cloud-managed surveillance closes it by shifting firmware updates, encryption, and access control from manual IT tasks to automated infrastructure. According to a Rhombus survey, 81.1% of physical security professionals now rank cybersecurity as a high or very high priority when evaluating surveillance systems. The question is whether your current architecture can actually deliver on that priority.
The On-Premise Security Problem
On-premise NVR and DVR systems were designed for a simpler threat landscape. They sit on local networks, store footage to local drives, and depend on manual maintenance to stay current. That model creates structural vulnerabilities that compound over time.
Unpatched Firmware: The Biggest Risk
The most dangerous weakness in on-premise surveillance is the firmware update gap. Patches require manual identification, download, testing, and deployment across every device. In practice, most organizations fall behind. Some never patch at all.
The consequences are not theoretical. In April 2026, FortiGuard Labs documented an active campaign called Nexcorium, a Mirai botnet variant exploiting CVE-2024-3721, an OS command injection vulnerability in TBK DVR-4104 and DVR-4216 devices. The malware targets ARM, MIPS R3000, and x86-64 architectures, establishes persistence through startup scripts and cron jobs, and conscripts compromised devices into large-scale DDoS infrastructure. Fortinet noted that IoT devices are increasingly prime targets for large-scale attacks due to their widespread use, lack of patching, and often weak security settings.
Nexcorium is not an isolated case. In November 2025, the Aisuru botnet compromised more than 700,000 camera and CCTV devices globally. These are not edge-case attacks. They represent a systemic pattern: threat actors scan for known vulnerabilities in DVR/NVR firmware, and the devices are reliably unpatched.
Other Structural Weaknesses
Default credentials remain a persistent problem. Many NVR and DVR devices ship with factory usernames and passwords that are never changed, giving attackers a trivially easy entry point.
Port forwarding creates direct internet exposure. Remote access to on-premise systems typically requires opening inbound ports or configuring VPNs, both of which expand the attack surface. Misconfigured port forwarding is one of the most common ways surveillance devices end up exposed on the open internet.
End-of-life hardware receives no updates. Manufacturers stop releasing firmware for older NVR and DVR models, leaving them permanently vulnerable to any newly discovered exploit. The TBK devices targeted by Nexcorium are a textbook example.
On-premise recorders also store footage at the same location being monitored. A fire, flood, or break-in can destroy the very evidence the system was meant to capture. If someone steals the NVR during a burglary, the footage of that burglary goes with it.
Why Cloud Surveillance Is More Secure
Cloud-managed surveillance addresses each of these weaknesses at the infrastructure level. On-premise systems depend on IT teams to maintain security device by device. Cloud platforms enforce protections automatically across every camera in a deployment.
Automatic Firmware Updates
Cloud platforms push firmware and security patches to every connected device simultaneously, with no IT intervention required. When a vulnerability is discovered, Rhombus can push patches to every camera in the fleet at once, dramatically shrinking the exposure window compared to manual on-premise patching cycles that often stretch months or longer. There is no manual download step, no compatibility testing across different device models, no reliance on an overstretched IT team remembering to prioritize camera firmware over the dozen other systems competing for their attention.
Rhombus delivers automatic firmware updates to every camera in the fleet, ensuring devices are always running the latest cybersecurity protections. The Nexcorium campaign targeted devices that had been vulnerable for nearly two years. Automatic updates close known vulnerabilities across an entire fleet in hours rather than months.
End-to-End Encryption
Cloud platforms encrypt video data both in transit and at rest. Even if data is intercepted during transmission or storage infrastructure is compromised, the footage remains unreadable without the proper decryption keys.
Rhombus takes encryption a step further with key segregation and rotation, meaning that even if a single encryption key were compromised, all other keys remain secure. On-premise NVR systems can technically support encryption, but few enforce it by default. Whether footage is actually encrypted depends entirely on the IT team configuring and maintaining that protection, and in practice, most on-premise deployments store video unencrypted on local hard drives. Cloud platforms remove that dependency by making encryption a default, always-on property of the system.
Enterprise Cloud Infrastructure
Where your data lives matters. Rhombus runs its cloud environment on Amazon Web Services (AWS), which provides a secure and resilient foundation for video storage and management. AWS maintains its own ISO 27001, SOC 2, and FedRAMP certifications across its global data center network. Rhombus builds on top of that certified foundation, meaning customers benefit from AWS’s physical data center security, redundancy, and compliance controls as part of a shared-responsibility model. AWS secures the underlying infrastructure; Rhombus secures the application, data handling, and access controls that run on it.
For IT managers evaluating cloud surveillance, the infrastructure question is worth asking directly: where is the data hosted, and what certifications does that infrastructure carry? A vendor running on a tier-one cloud provider with independent certifications offers a level of infrastructure security that no single-site on-premise deployment can match.
SOC 2 Audited Controls
SOC 2 is a compliance framework that evaluates how organizations protect customer data across security, availability, processing integrity, confidentiality, and privacy. SOC 2 common criteria, including CC6.7, address logical access controls and protections around data transmission and storage. While CC6.7 does not prescribe specific technologies, encryption of data at rest and in transit is a widely expected control under this criterion and a standard expectation during SOC 2 audits. An independent CPA firm performs the audit and validates that the vendor’s security controls are not just documented but actually functioning.
Rhombus is SOC 2 audited, which means its encryption practices, access controls, and incident response procedures are independently verified on a regular basis. On-premise NVR and DVR deployments rarely have equivalent external validation. Their security posture depends almost entirely on internal IT practices, with no third party confirming whether controls are adequate or even in place.
No Exposed Local Servers
Cloud-managed cameras connect outbound to the cloud platform. They do not require open inbound ports, port forwarding, or exposed local servers. The camera authenticates to the cloud; the user authenticates to the cloud. No inbound ports or direct device-to-user network paths are required by the architecture.
This outbound-only design produces a dramatically smaller attack surface. On-premise remote access typically requires VPN configuration (complex and often misconfigured), port forwarding (directly exposing the device to the internet), or dynamic DNS services (adding yet another potential attack vector). Cloud architecture sidesteps all three.
Centralized Access Control and Audit Logs
Cloud platforms provide centralized user management with role-based access control. Administrators can add or remove users instantly from any location, set granular permissions by camera, location, or time range, enforce multi-factor authentication, and review complete audit logs showing who accessed what footage and when.
On-premise systems often lack these capabilities entirely. Limited user management, no centralized audit logging, and no efficient way to revoke access when an employee leaves the organization. In regulated industries, the inability to produce a comprehensive access log creates compliance exposure on top of the immediate security risk.
Disaster Recovery and Redundancy
Cloud storage is geographically redundant by design. Footage is replicated across multiple data centers, so a fire, flood, or physical breach at the monitored facility does not result in lost evidence. The recording of the incident itself is safely stored offsite and accessible from any authorized device.
Building equivalent redundancy on-premise means the organization must design, fund, and maintain its own offsite replication. Most don’t.
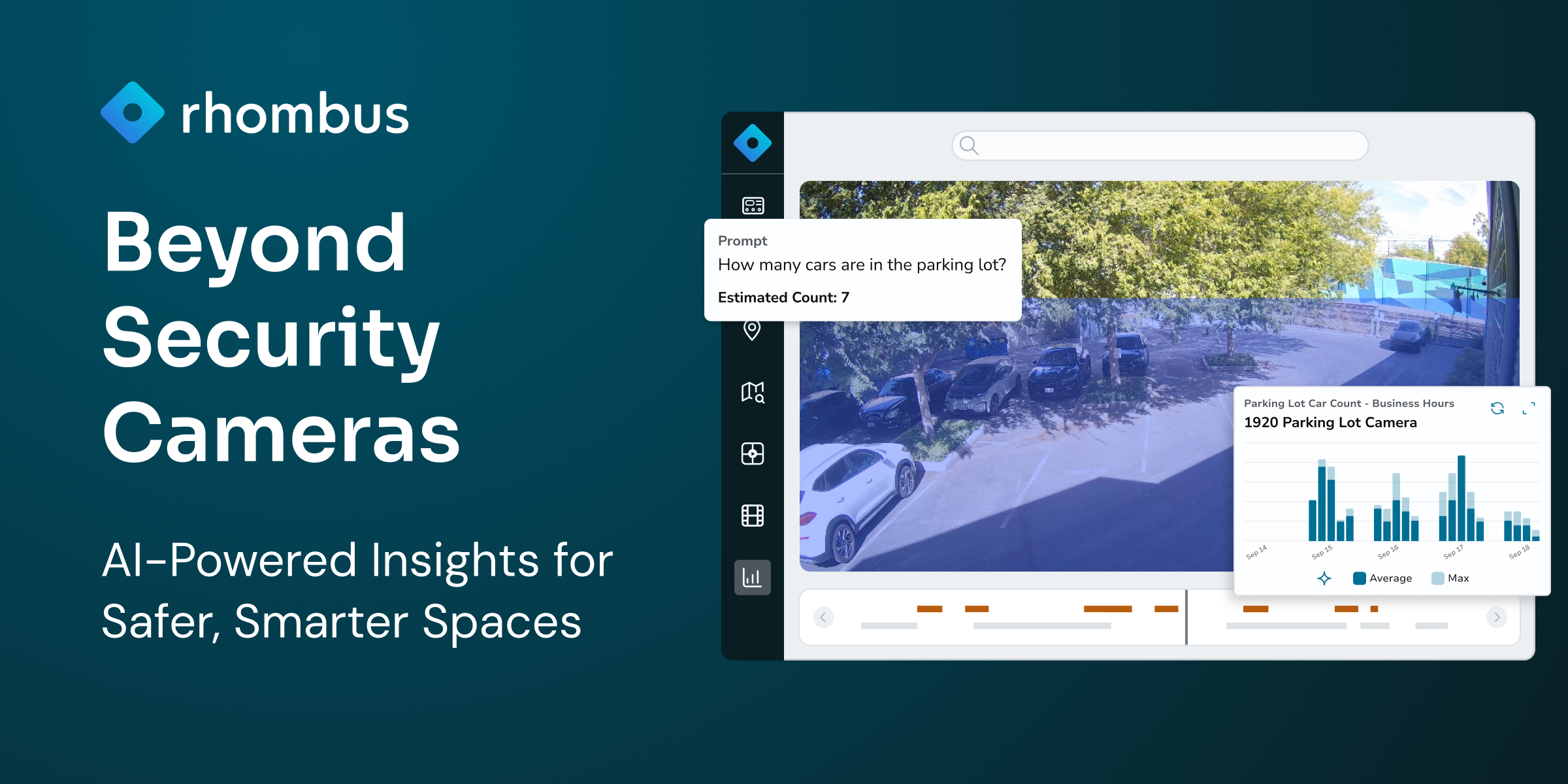
The Cloud-Edge Advantage
A common concern about cloud surveillance is latency and bandwidth. If all video processing happens in the cloud, what happens during a network outage? Does the system consume excessive bandwidth?
Well-architected cloud platforms answer this with a hybrid approach. Rhombus uses a cloud-edge architecture where cameras process video locally at the edge. Analytics, motion detection, and recording continue to function even if the internet connection drops temporarily. Management, long-term storage, and remote access are handled in the cloud.
This model delivers the reliability of local processing (low latency, offline operation, minimal bandwidth consumption) alongside the security advantages of cloud infrastructure (encryption, automatic updates, redundant storage, centralized access control). It combines the strongest properties of each approach without forcing a tradeoff.
What to Look for in a Cloud Surveillance Vendor
If you are evaluating cloud-managed surveillance platforms, these are the security criteria that matter most:
Automatic firmware updates should be a baseline requirement. Any vendor that requires manual patching is replicating the core vulnerability of on-premise systems.
Encryption standards should cover data at rest and in transit, with key rotation and segregation as additional safeguards.
Compliance certifications provide external validation. Look for SOC 2 audited controls at a minimum, along with NDAA and TAA compliant hardware if you operate in government or regulated sectors.
Zero Trust architecture means no user or device is inherently trusted. Every access request is verified, every session is authenticated, and no single compromised credential grants unlimited access.
Data access policies matter. Ask whether the vendor’s own employees can access your video data. The strongest vendors, including Rhombus, enforce a no super-admin policy where system access must be explicitly granted by the customer. There is no backdoor.
Infrastructure transparency is a signal of maturity. A vendor should be willing to tell you where your data is hosted and what certifications that infrastructure carries.
Frequently Asked Questions
Is cloud surveillance more secure than on-premise? Yes. Cloud-managed surveillance platforms enforce automatic firmware updates, end-to-end encryption, and centralized access controls across every device in a deployment. On-premise NVR and DVR systems depend on manual maintenance for each of these protections, and the track record of real-world attacks shows that manual patching consistently falls behind.
What are the risks of on-premise NVR systems? On-premise NVR systems are vulnerable to unpatched firmware exploits, default credential attacks, physical theft of the recorder and its footage, and misconfigured port forwarding that exposes devices to the internet. End-of-life hardware that no longer receives manufacturer updates compounds these risks over time.
Does cloud video surveillance encrypt footage? Reputable cloud surveillance vendors encrypt video data both in transit and at rest. Rhombus, for example, uses key segregation and rotation so that a single compromised key does not expose footage across the system.
What is cloud-edge architecture in surveillance? Cloud-edge architecture processes video locally on the camera itself while using the cloud for management, long-term storage, and remote access. This approach keeps cameras functional during internet outages and minimizes bandwidth consumption while still delivering the security benefits of cloud infrastructure.
What compliance certifications should I look for in a cloud surveillance vendor? SOC 2 is the most important baseline, as it requires independent verification of a vendor’s security controls. NDAA and TAA compliance matter for government and regulated environments. You should also confirm that the vendor’s hosting infrastructure (such as AWS) carries its own certifications like ISO 27001 and FedRAMP.
Conclusion
Every major vulnerability in on-premise surveillance, unpatched firmware, exposed local servers, absent external audits, physical theft risk, traces back to the same root cause: security that depends on manual effort by individual IT teams will eventually fall behind. Active threat campaigns like Nexcorium and Aisuru are proving that right now, at scale, across hundreds of thousands of devices.
Cloud-managed surveillance shifts those responsibilities to infrastructure. Automatic updates close vulnerabilities in hours. End-to-end encryption is a default, not a configuration choice. SOC 2 audits verify controls that on-premise deployments rarely validate. Outbound-only connectivity eliminates the exposed ports that attackers scan for. Geographically redundant storage means evidence survives the incidents it captures.
Rhombus was built by cybersecurity professionals around these principles: Zero Trust architecture, enterprise-grade encryption, and cloud-edge processing on AWS infrastructure. If you’re weighing whether cloud surveillance can meet your security requirements in practice, requesting a demo is the most direct way to pressure-test that question.