Your Cameras Are Computers. We Built a Security Company That Acts Like It.
The box in the closet is dead.
A decade ago, physical security meant deadbolts and DVRs. A camera was a camera. A lock was a lock. The most sophisticated thing in the system was the person watching the monitors.
That world doesn’t exist anymore.
Today, every camera on your network is an edge computing device. Every badge reader is an identity endpoint. Every sensor streams data to the cloud 24/7.
The devices evolved — and the attack surface evolved with them.
Yet much of the industry still builds security products like it’s 2012: default passwords, manual firmware updates, encryption added later. The result is predictable. Physical security hardware becomes the weakest link in an otherwise modern IT environment.
An insecure camera is not just a privacy problem. It can become a foothold into your corporate network. A misconfigured access controller is not an operational oversight. It’s an identity vulnerability.
The distinction between physical and cybersecurity isn’t blurry anymore – it’s gone.
At Rhombus, we don’t ignore that reality.
We are not a security company that ships boxes and checks compliance boxes. We operate a security platform – and that means we are entrusted with something heavier than devices.
We are entrusted with trust.
“The default password is the original sin.”
Legacy physical security treated device hardening as someone else’s problem. Ship it with admin/admin. Let the integrator figure it out. Hope nobody scans for open ports.
We rejected that model.
No default passwords. Every Rhombus device ships uniquely secured out of the box. There are no factory credentials waiting to be forgotten.
Automatic firmware updates. Security patches deploy proactively to address vulnerabilities in a timely manner – without requiring manual intervention.
Tamper detection. If a device is physically interfered with, the system generates alerts. Integrity does not depend on someone noticing a disconnected cable.
Security is not step two. It is step one.
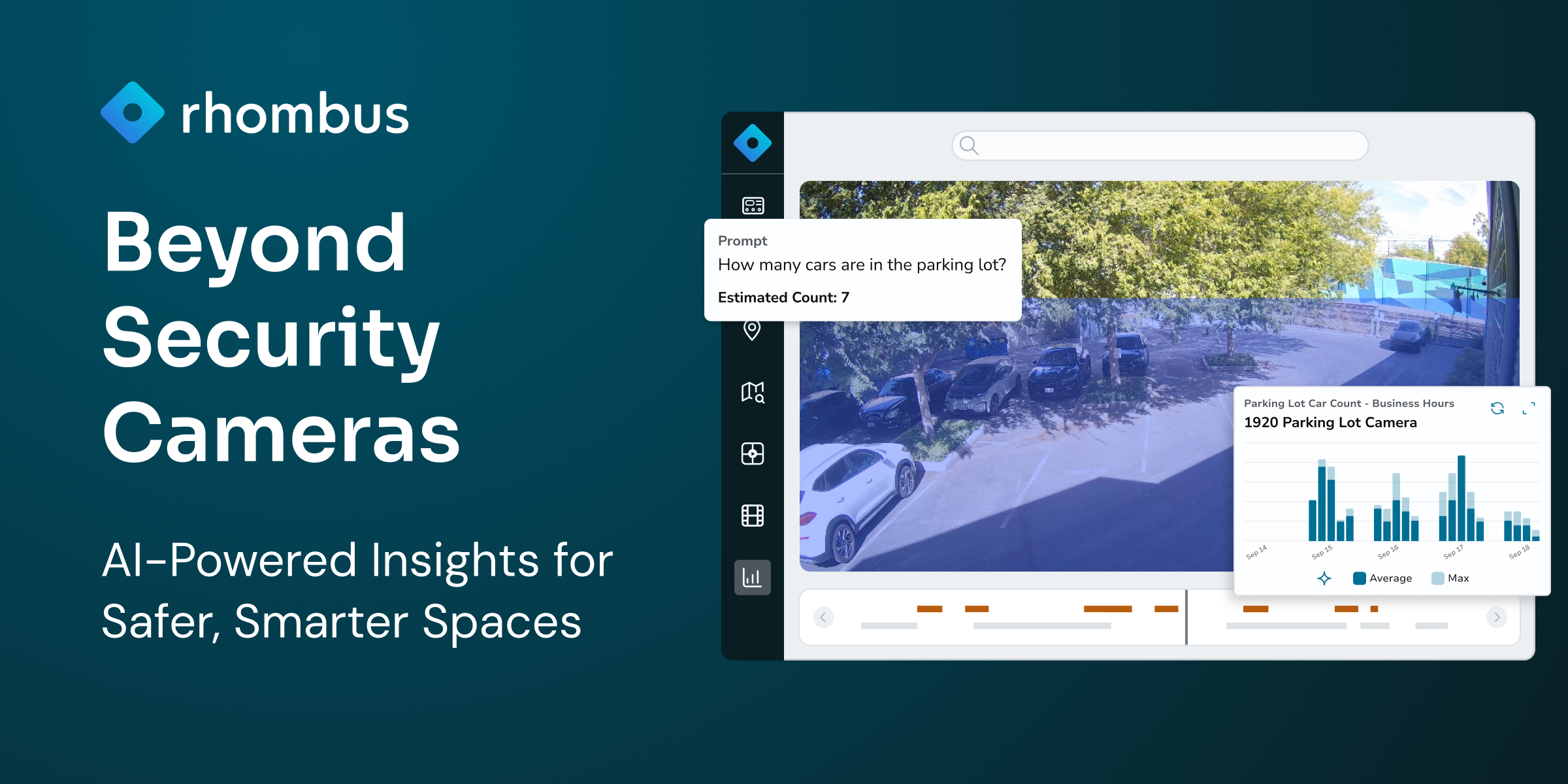
“Your footage is operational intelligence. We treat it that way.”
Video and access records don’t just show what happened. They reveal how your organization moves, operates, and responds.
That data deserves the same rigor as any other critical system.
Encryption in-transit and at-rest. Data is encrypted on-device, in-transit, and at-rest using industry-standard protocols. Your data is protected at every stage of its lifecycle.
Cloud-native architecture. The Rhombus Platform is built on resilient infrastructure designed for durability, redundancy, and real-world threat models – not checkbox compliance.
Logical tenant isolation. Customer environments are logically segregated to prevent cross-tenant access.
Continuous vulnerability management. We perform automated vulnerability scanning across our codebase and production infrastructure. Findings are risk-ranked and remediated under defined timelines.
Independent penetration testing. At least annually, we engage independent third-party firms to simulate real-world attacks against our applications and infrastructure. The goal is simple: find it before someone else does.
At Rhombus, we believe in talking the talk and walking the walk. Security is not layered onto the platform. It is embedded into how it is built, operated, and continuously improved.
“Security without privacy is surveillance.”
Monitoring technology is advancing faster than policies governing it.
We believe the controls around who can see what matter as much as the cameras themselves.
Granular role-based access controls. Customers define precisely who accesses what — and the system enforces it.
Comprehensive audit logging. Every system action is recorded. Accountability isn’t optional.
Responsible AI practices. AI and analytics capabilities are customer-controlled, governed by published acceptable use and privacy policies. We don’t make decisions about your data for you.
“Claims are easy. Audits are not.”
Anyone can publish a blog post about how seriously they take security.
The harder question is whether you are willing to let independent auditors test your controls over time – and publish the results.
We did.
Rhombus recently completed a multi-month independent audit of our security controls and operational practices and achieved a 12-month SOC 2 Type 2 attestation.
This is not a point-in-time assessment. SOC 2 Type 2 evaluates whether controls operate effectively over a sustained period. Independent auditors tested our processes across engineering, infrastructure, access management, change management, and operational controls.
The result reflects discipline embedded across the entire organization – from Engineering and IT to HR, Legal, Finance, and Support.
It was not a security team project. It was a company commitment.
“This is not the finish line.”
SOC 2 Type 2 is one validation of our work, but it is not the destination.
As a security company, we hold ourselves to the same standard of rigor we expect from the systems protecting your people and facilities. That obligation doesn’t simply expire when the audit report is signed.
Physical security is no longer just physical.
It is software.
It is infrastructure.
It is identity.
It is data.
Securing it demands architecture, governance, and accountability – not just hardware.
We will continue strengthening the Rhombus Platform against evolving threats.
And we will continue earning the trust you place in us – not by talking about it, but by proving it.