Putting Customer Privacy and Security First
For more information on cybersecurity and privacy best practices in a video security context, see: The Ultimate Guide to Cybersecurity for Cloud Video Surveillance & IP Security Cameras.
Recently, there were published reports that a video security company, Verkada, suffered a breach where hackers gained access to live feeds of 150,000 Verkada cameras and other sensitive customer information. We want to assure everyone that the methods used to compromise Verkada’s devices and infrastructure cannot happen to Rhombus Systems.
Rhombus has always maintained a ‘Security First’ approach. Before starting Rhombus Systems, the founding team created Mojave Networks, a cybersecurity company acquired by Sophos. With decades of cybersecurity experience, the Rhombus design and engineering workflows all begin with security. Rhombus does not have any type of super admin or god-mode account that allows access to every customer account. Security and privacy are intrinsic elements of the Rhombus solution and are designed to protect it against the most sophisticated attacks.
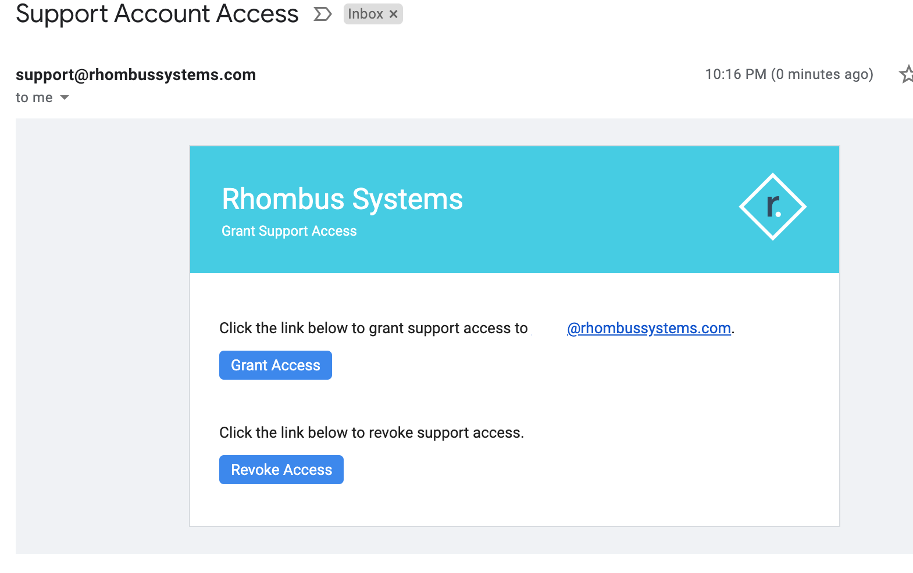
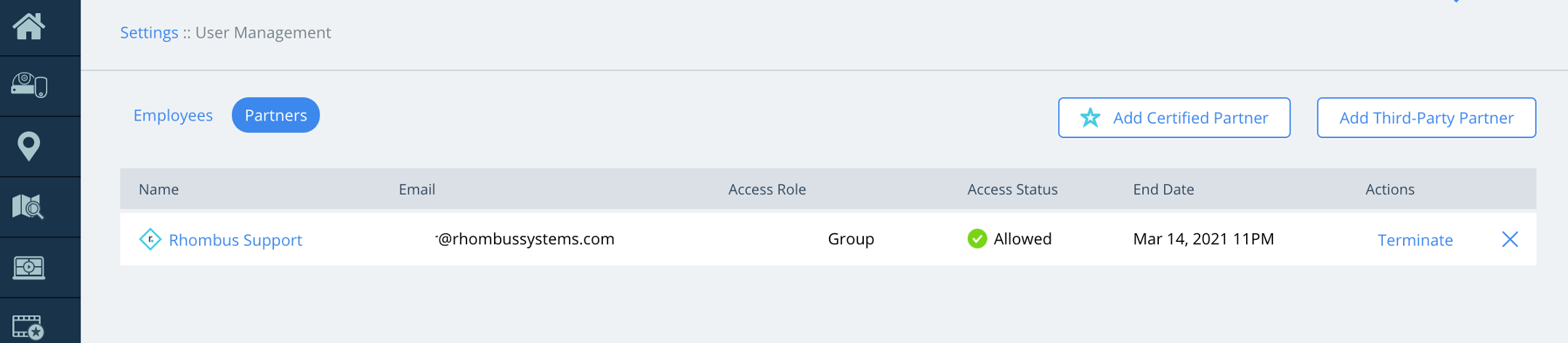
Furthermore, it is a core tenet of Rhombus that customers, and only customers, control access to their data. No one at Rhombus Systems has access to any customer video data. There are no ‘backdoors.’ Even when contacting Rhombus Support, customers must intentionally grant access (for a limited amount of time) to Rhombus Support engineers.
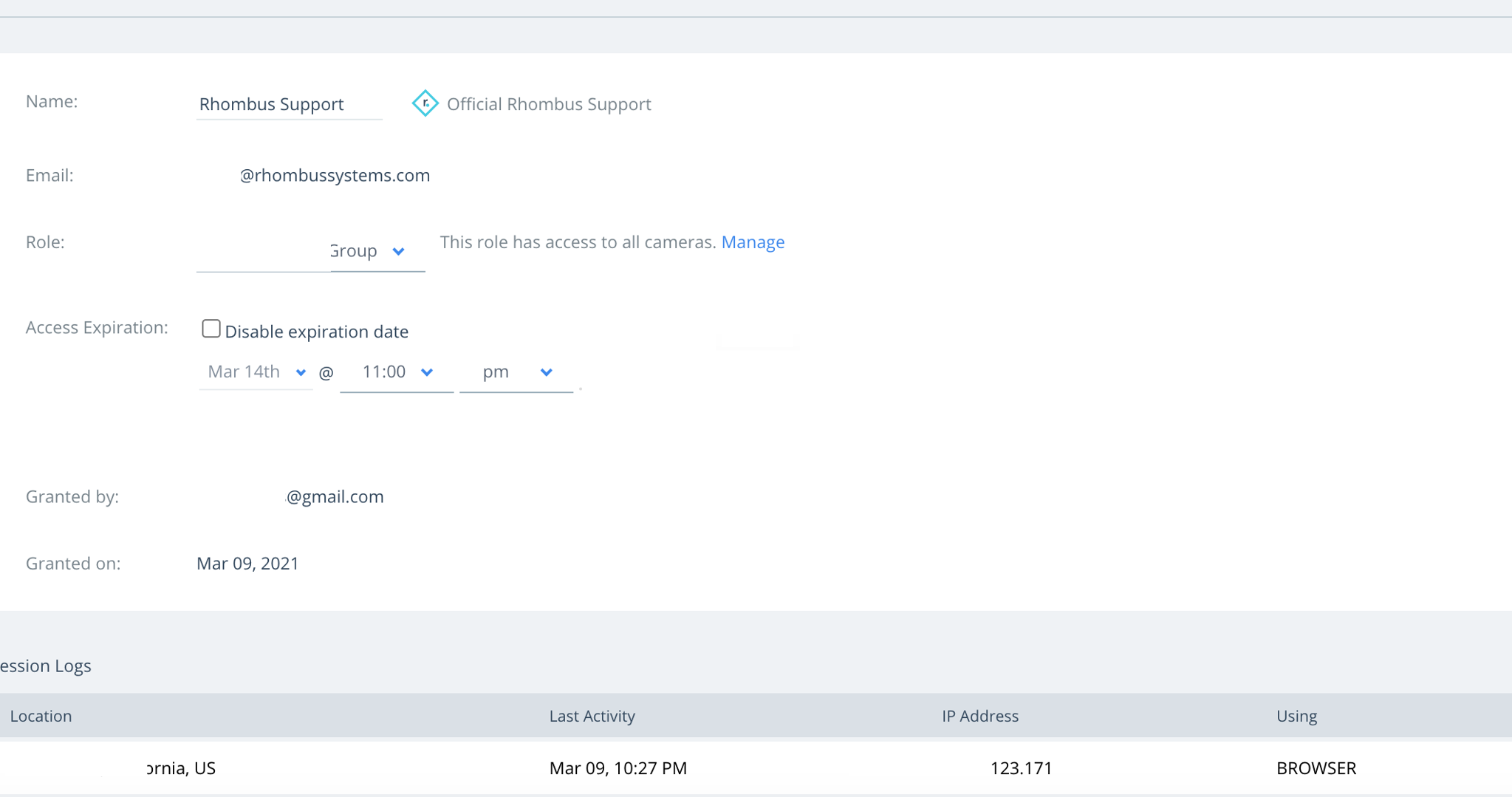
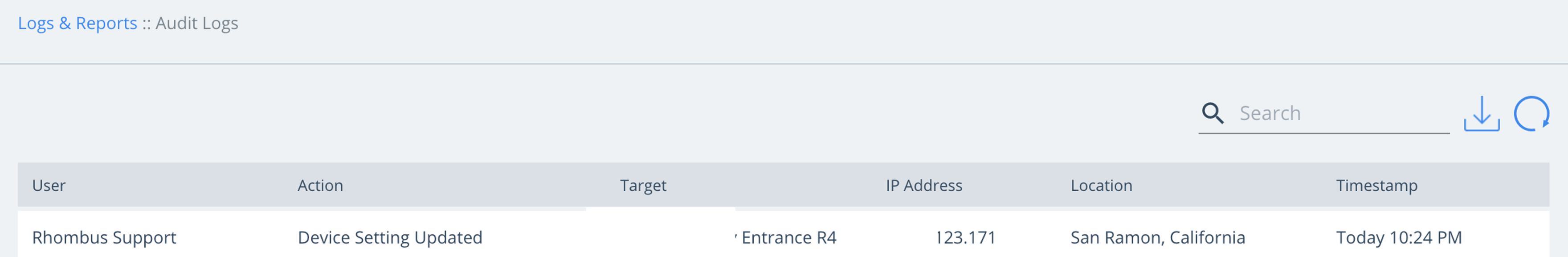
Here is an illustration of how customers can securely and with complete transparency, grant, revoke, and monitor Rhombus Support access at all times with the corresponding audit trail.
Grant and revoke support access via email
Grant and revoke support access via the Rhombus Console
Monitor Rhombus Support access sessions details
Monitor audit logs
We realize these types of events can create a lot of uncertainty. The choices made by one company do not reflect the industry best-practices nor are they consistent with the ‘Security First’ approach employed by Rhombus Systems:
- Rhombus DOES NOT have any type of super admin account that allows access to customer accounts
- Only authorized end users have the authority to initiate and provide account access to Rhombus Support, Certified Partners, or Third-Party Partners
- All granted access is logged and can be revoked at any time
- Rhombus employees have limited access to necessary systems and are required to use 2-factor authentication and industry-leading SSO
- SMS 2FA is disabled for all Rhombus employees due to vulnerabilities
- Rhombus automatically monitors for any suspicious and anomalous logins with automatic alerts sent directly to the customer when these are detected
- No Rhombus infrastructure access relies solely on username and password and all internal infrastructure requires 2FA tokens that change every 30 seconds
All of us at Rhombus Systems understand the trust placed in our products. Our intent with being open and transparent about our security and privacy practices is to demonstrate that your trust in Rhombus is well-founded. If you have any questions regarding how to protect privacy and security, please email us at sales@rhombussystems.com at any time.